CTO at NCSC Summary: week ending December 3rd
Guidelines for secure AI system development are go.. lets minimise technical security debt ..
Welcome to the weekly highlights and analysis of the blueteamsec subreddit (and my wider reading). Not everything makes it in, but the best bits do.
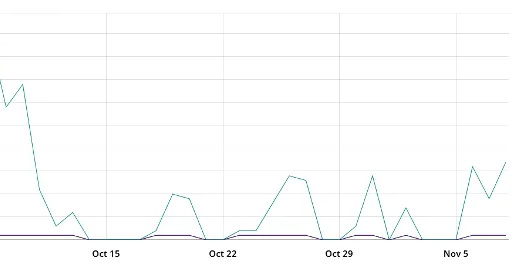
Operationally this week nothing of note beyond the usual background noise.
In the high-level this week:
Guidelines for secure AI system development - by NCSC UK and CISA along with co-signatories from many others - Guidelines for providers of any systems that use artificial intelligence (AI), whether those systems have been created from scratch or built on top of tools and services provided by others.
NIS Investments Report 2023 - 42% of OES/DSPs have subscribed to a dedicated cyber insurance solution in 2022, up from 30% last year, though only 13% of SMEs subscribe to cyber insurance
The Department of the Navy releases inaugural Cyber Strategy - The seven lines of effort in this strategy are improve and support the cyber workforce; defend enterprise IT, data, and networks; secure Defense Critical Infrastructure and weapon systems; conduct and facilitate cyber operations; partner to secure the Defense Industrial Base; and foster cooperation and collaboration.
US Army publishes first doctrinal manual dedicated to information - codifies the Army’s approach to the military uses of data and information, and recognizes all activities generate informational effects that can contribute to, or hamper, achieving objectives
EU Cyber solidarity act - the Commission has proposed a regulation on a cyber solidarity act that would address the urgent need to strengthen solidarity and EU capacities to detect, prepare for and respond to cybersecurity threats and incidents.
EU cybersecurity exercise: foster cooperation, secure free and fair EU elections - It took place in the European Parliament and was organised by the European Parliament’s services, the European Commission and the EU Agency for Cybersecurity (ENISA).
Swiss digital ID scheme could begin in 2026 - Almost three years after Swiss voters rejected a private e-ID scheme at the ballot box, the Federal Council has presented its proposal for the introduction of a state-run system
Which Cyber Regulations Fit Which Sectors? - Cyber regulation is needed because the markets have failed to deliver security. The government and outside researchers still have a lot of homework to do to ensure regulations are correctly targeted for the best chance of success with the least cost of compliance.
A [Canadian] Cyber Defence Review - DND/CAF Departmental Results 2022-2023 - National Defence assumed an assertive posture in the cyber domain to ensure the ability to defend against malicious cyber actors and potential adversaries, as well as improve the capability to conduct offensive cyber operations.
‘SIM Swapper’ Sentenced to Eight Years in Prison for Campaign of Fraud and Deception, Including Hacking into Instagram Accounts - A downtown Los Angeles man was sentenced today to 96 months in federal prison for committing a series of frauds, including one in which he “SIM swapped” victims – one of them a social media influencer – to hijack their Instagram accounts to unlawfully obtain money.
The operator of a data recovery company who extorted 2.6 billion won from 730 hacking victims (Korean) - was arrested and indicted
Defence Intelligence of Ukraine conducted a cyber operation against Rosaviatsia - sanctions accelerate Russia's aviation collapse - as a result of a successful complex special operation in cyberspace, a large volume of confidential documents of the structural subdivision of the Russian Ministry of Transport - the Federal Air Transport Agency (Rosaviatsia) - is now acquired.
Report: The attack against Danish, critical infrastructure Report about the largest cyber attack against Danish, critical infrastructure we know of - 22 companies, that operate parts of the Danish energy infrastructure, were compromised in a coordinated attack (English report now).
Europe’s grid is under a cyberattack deluge, industry warns - Europe’s grid operators share the concerns. Damian Cortinas, who chairs the board of the EU’s electricity network association ENTSO-E, told a POLITICO event last week that tackling cyberattacks is an especially “high priority” for operators due to how interconnected Europe’s power systems are.
North Korean agent uses Japanese companies to obtain foreign currency...Police declares it an ``espionage incident'' - Police authorities have said that North Korean agents based in China are suspected of using Japanese companies to help North Korea acquire foreign currency
Treasury Sanctions Mixer Used by the DPRK to Launder Stolen Virtual Currency - Sinbad has processed millions of dollars’ worth of virtual currency from Lazarus Group heists, including the Horizon Bridge and Axie Infinity heists. Sinbad is also used by cybercriminals to obfuscate transactions linked to malign activities such as sanctions evasion, drug trafficking, the purchase of child sexual abuse materials, and additional illicit sales on darknet marketplaces.
Reporting on/from China
Espionage: Chinese hacker group was in the network of the Dutch chip manufacturer NXP for years - for almost two and a half years, from the end of 2017 to spring 2020, cyber spies had access to the computer systems of the Dutch chip manufacturer.
Chinese censorship following the death of Li Keqiang - Our results demonstrate China’s ongoing efforts to push state-sanctioned narratives concerning politically sensitive topics, impacting the integrity of the online information environment.
Friendly foreign influencers win growing following in China - ASPI said influencers were part of a Chinese strategy of “market-enabled propaganda production” that was “likely to have significant implications for the global information landscape”.
China’s New(ish) SW26010-Pro Supercomputer at SC23 - The result is a chip that requires a lot of optimization effort from the compiler or programmer.
Artificial intelligence
FTC Authorizes Compulsory Process for AI-related Products and Services - has approved an omnibus resolution authorizing the use of compulsory process in nonpublic investigations involving products and services that use or claim to be produced using artificial intelligence (AI) or claim to detect its use.
A New Landmark for Consumer Control Over Their Personal Information: CPPA Proposes Regulatory Framework for Automated Decisionmaking Technology - The draft also proposes potential options for additional consumer protections around the use of their personal information to train these technologies.
AI Act: MEPs close ranks in asking for tighter rules for powerful AI models - In this late phase of the negotiations, EU policymakers have been butting heads on the approach for foundation models, powerful types of AI like OpenAI’s GPT-4, which powers the world’s most famous chatbot, ChatGPT.
Putin says West cannot have AI monopoly so Russia must up its game - Moscow has ambitions to be an AI power too, but its efforts have been set back due to the war in Ukraine which prompted many talented specialists to leave Russia and triggered Western sanctions that have hindered the country's high-tech imports.
India warns Facebook, YouTube to enforce rules to deter deepfakes - The warning was conveyed by deputy IT minister Rajeev Chandrasekhar in a closed-door meeting where he said many companies had not updated their usage terms despite 2022 rules that prohibit content "harmful" to children, obscene or that "impersonates another person".
New AI Strategy and an Artificial Intelligence (Development & Regulation) Bill for India: Proposal - a third party proposal.
ChatGPT Has Been Turned Into A Social Media Surveillance Assistant - Social Links, a surveillance company that had thousands of accounts banned after Meta accused it of mass-scraping Facebook and Instagram, is now using ChatGPT to make sense of data its software grabs from social media.
Cyber proliferation
Spyware: MEPs slam insufficient EU response to abuse - With 425 votes in favour, 108 against, and 23 abstaining, the European Parliament on Thursday adopted a resolution on the lack of follow-up to Parliament’s proposals following its inquiry into the use of Pegasus and equivalent surveillance spyware.
Spyware attack attempts on mobile devices of members of civil society discovered - On October 30, two members of civil society from Belgrade received an alert from Apple that they were potential targets of state-sponsored technical attacks.
Spyware Targeting Against Serbian Civil Society - reporting on the same
Stanford Emerging Technology Review - A report on ten key technologies and their policy implications.
Reflections this week stem from the observation that the level of maturity in Operational Technology threat intelligence and incident response capabilities and capacity/experience are likely not where they need to be. The diversity of suppliers and configurations coupled with the challenges around getting access to the technology to perform research presents challenges which we will want to overcome. Planning for a ‘when’ event and not an ‘if’ with respect to these technologies instinctively seems like the level of preparedness we want.
Enjoying this? Don’t get via e-mail? Subscribe:
Think someone else would benefit? Share:
All attribution is by others and not the UK Government, please see the legal text at the end.
Have a lovely Thursday
Ollie
Cyber threat intelligence
Who is doing what to whom and how.
Reporting on Russia
Cyber spies from XDSpy attack Russian metallurgists and military-industrial complex enterprises
Cyber operation reporting around one being run in Russia using what appears to be phishing for initial access..
Yesterday, November 22, and the day before yesterday, November 21, malicious mailings were discovered targeting the mail of one of the Russian metallurgical enterprises, as well as a research institute engaged in the development and production of guided missile weapons.
Reporting on China
New SugarGh0st RAT targets Uzbekistan government and South Korea
Ashley Shen and Chetan Raghuprasad provide reporting which indicates evolution in a specific implant family.
[We] recently discovered a malicious campaign that likely started as early as August 2023, delivering a new remote access trojan (RAT) we dubbed “SugarGh0st.”
We found evidence suggesting the threat actor is targeting the Uzbekistan Ministry of Foreign Affairs and users in South Korea.
We assess with high confidence that the SugarGh0st RAT is a new customized variant of Gh0st RAT, an infamous trojan that’s been active for more than a decade, with customized commands to facilitate the remote administration tasks as directed by the C2 and modified communication protocol based on the similarity of the command structure and the strings used in the code.
We observed two infection chains leveraging Windows Shortcut embedded with malicious JavaScript to deliver the components to drop and launch the SugarGh0st payload.
In one infection chain, the actor leverages the DynamixWrapperX tool to enable Windows API function calls in malicious JavaScript for running the shellcode.
Talos assesses with low confidence that a Chinese-speaking threat actor is operating this campaign based on the artifacts we found in the attack samples.
https://blog.talosintelligence.com//new-sugargh0st-rat/
Reporting on North Korea
Crypto Country: North Korea’s Targeting of Cryptocurrency
Analysis of supposed crypto operations and their scale.
Anyone operating in the cryptocurrency industry — individual users, exchange operators, and financiers with a portfolio of startups — should be aware of the potential to be targeted by North Korean threat actors. Entities operating in the traditional finance space should also be on the lookout for North Korean threat group activities. Once cryptocurrency is stolen and converted into fiat currency, North Korean threat actors funnel the funds between different accounts to obscure the source. Oftentimes stolen identities, along with altered photos, are used to bypass anti-money-laundering and know-your-customer (AML/KYC) verification
https://go.recordedfuture.com/hubfs/reports/cta-2023-1130.pdf
Malicious OLE injection attack inside HWP document
FlowerPower APT campaign uses Github C2
Reporting from South Korea on a campaign which uses Github for its command and control. Other than that the tradecraft is run-of-the-mill.
Using deceptive approaches through foreign news channel interviews, etc., using HWP document delivery method including malicious OLE
Execute encrypted PowerShell commands using the FlowerPower APT attack tool series
Set GitHub, a code hosting platform for development version management and collaboration, as a threat command base.
North Koreans use fake names, scripts to land remote IT work for cash
James Pearson provides reporting on this operation which gives a sense as the geographies of the alleged victims.
Reuters found further evidence in leaked darkweb data that revealed some of the tools and techniques used by North Korean workers to convince firms to employ them in jobs as far afield as Chile, New Zealand, the United States, Uzbekistan and the United Arab Emirates.
The documents and data reveal the intense effort and subterfuge undertaken by North Korean authorities to ensure the success of a scheme that has become a vital lifeline of foreign currency for the cash-strapped regime.
DPRK Crypto Theft | macOS RustBucket Droppers Pivot to Deliver KandyKorn Payloads
Phil Stokes issues reporting showing that they are mixing up their tooling and appear to have crossed various streams.
Our analysis of further activity in these campaigns suggests that DPRK threat actors are now ‘mixing and matching’ components from these operations, with SwiftLoader droppers being used to deliver KandyKorn payloads.
Kimsuky targets domestic research institutes by disguising import declarations
South Korean reporting on what they suspect is North Korean activity, the novelty here are the file type used in this campaign.
[We] recently confirmed that malicious JSE files disguised as import declarations were being distributed targeting domestic research institutes by the Kimsuky attack group. The attacker ultimately uses the backdoor to steal information and execute commands.
Konni Campaign Distributed via Malicious Document
Cara Lin details a malicious document campaign which is asserted as having a North Korean origin. The tradecraft is rather basic..
This campaign relies on a remote access trojan (RAT) capable of extracting information and executing commands on compromised devices. Operating for several years, this campaign employs diverse strategies for initial access, payload delivery, and establishing persistence within victims' networks. In this blog, we will elaborate on the behavior of the malware at each stage.
https://www.fortinet.com/blog/threat-research/konni-campaign-distributed-via-malicious-document
Reporting on Iran
Unveiling the Persisting Threat: Iranian Mobile Banking Malware Campaign Extends Its Reach
Aazim Yaswant and Vishnu Pratapagiri give an interesting insight into alleged regional targeting by a threat one might not expect. Also hints at being enduring..
In July 2023, it was discovered that an Android mobile campaign, which consisted of banking trojans, was targeting major Iranian banks.
[We] recently found that the campaign not only remains active but also extended its capabilities. These newly found samples are completely undetected by the industry. At the same time, evidence was found linking this threat actor to phishing attacks targeting the same banks.
Reporting on Other Actors
WildCard: The APT Behind SysJoker Targets Critical Sectors in Israel
Nicole Fishbein provides insight to a threat actor who is allegedly targeting Israeli CNI.
Our research team has identified a new APT group, dubbed “WildCard,” initially detected through its use of the SysJoker malware, which targeted Israel’s educational sector in 2021. WildCard has since expanded its reach, creating sophisticated malware variants disguised as legitimate software, and a recently developed malware called ‘RustDown,’ written in Rust for potential operational advantages. Connections to Operation ElectricPowder indicate WildCard’s advanced capabilities with a focus on critical sectors within Israel.
https://intezer.com/blog/research/wildcard-evolution-of-sysjoker-cyber-threat/
Israel-Hamas War Spotlight: Shaking the Rust Off SysJoker
Further reporting on the same campaign..
Among the most prominent changes is the shift to Rust language, which indicates the malware code was entirely rewritten, while still maintaining similar functionalities. In addition, the threat actor moved to using OneDrive instead of Google Drive to store dynamic C2 (command and control server) URLs.
Analysis of newly discovered variants of SysJoker revealed ties to previously undisclosed samples of Operation Electric Powder, a set of targeted attacks against Israeli organizations between 2016-2017 that were loosely linked to the threat actor known as Gaza Cybergang.
https://research.checkpoint.com/2023/israel-hamas-war-spotlight-shaking-the-rust-off-sysjoker/
Analysis of complex attacks targeting Syrian soldiers
Chinese reporting on a alleged attack again Syrian military. Interesting to see the end-to-end..
[We] detected a piece of malware disguised as a Syrian Development Trust Fund application.
It is a combined phishing and Trojan horse attack targeting Syrian soldiers and will steal the victim's private information and social account information.
The phishing page claims to be a new project of the Syrian Development Trust Fund to support heroes in the Syrian army, and requires filling in personal and family information, such as name, phone number, military rank, service location, wife’s name, children’s information, etc.
SpyMax's functions are very comprehensive, including monitoring SMS, accessing the microphone, recording audio and video, stealing address books and call records, stealing files, real-time location, etc.
This compound attack on Syrian soldiers is highly confusing, destructive, and difficult to trace. Once infected, it may even threaten the lives and property of the victims and their families.
Discovery
How we find and understand the latent compromises within our environments.
AD-Canaries
Quentin Arnould releases a script which will help those still running legacy onsite Windows Active Directory.
AD Canaries detection is based on
Directory Service Object Access : Failureaudit which generates a 4662 event in the Security eventlog on your domain controller upon AD enumeration behaviours (i.e access attempt on any canary object).
https://github.com/AirbusProtect/AD-Canaries
IMDSpoof
Graham Helton releases another piece of deception tech that will help impose cost on threat actors.
This tool spoofs that endpoint and redirects traffic sent to
169.254.169.254to a local webserver that serves fake data. This can be leveraged for highly tuned detections by inserting honey AWS tokens into the response of the spoofed IMDS response.
https://github.com/grahamhelton/IMDSpoof
Defence
How we proactively defend our environments.
The evolution of Windows authentication
Microsoft on a path to deprecate NTLM authentication in Windows
We are working on strengthening user authentication by expanding the reliability and flexibility of Kerberos and reducing dependencies on NT LAN Manager (NTLM).
Our end goal is eliminating the need to use NTLM at all to help improve the security bar of authentication for all Windows users.
Take action to stop domain fronting on your [Microsoft] application before 8 January 2024
First CDN killing off this offensive technique used to subvert detection by defence teams..
We’ve been making progressive changes to Azure Front Door and Azure CDN from Microsoft to align with our commitment to prevent domain fronting behavior. Starting from 8 January 2024, all existing Azure Front Door and Azure CDN Standard from Microsoft (classic) resources will block any HTTP request that exhibits domain fronting behavior. The block implementation will start roll out on 8 January 2024 and will take one week or two weeks for the change to roll out to all regions.
Fastly announces plans to block domain fronting in February 2024
Second CDN killing off this technique..
We will be forbidding domain fronting from happening by restricting it on a shared offset you might depend upon. This change will be applied during February 27th, 2024 .
https://github.com/net4people/bbs/issues/309
Really Useful Logging and Event Repository (RULER) Project
Phill Moore embarks on a knowledge management project which will be useful to many..
I was often coming across issues where I would see logs from different applications and thought there has to be a good way of recording what we should be looking for in a forensic investigation.
For example - what are the quick wins in a remote access application to identify when it was used. Or what types of useful information can be found for a specific anti-virus application (especially if it encodes the data)
The bulk of this is compiled from the references listed on each page. Full credit goes to everyone that put in a lot of hard work and tested each of these applications. It does take time to put together each resource and I'm very grateful to be able to help curate and centralise this knowledge in the hopes that it helps speed up investigations.
https://ruler-project.github.io/ruler-project/
Attack surface reduction rules reference
Can now block webshell creation on Exchange servers.
This rule blocks web shell script creation on Microsoft Server, Exchange Role.
Can now block execution of potentially obfuscated scripts.
This rule detects suspicious properties within an obfuscated script.
Incident Writeups
How they got in and what they did.
Security Bulletin NR23-01
No details yet of what is happening - so keep watching..
We value our New Relic community and want to make our customers aware of a recent cybersecurity incident that we are working diligently to investigate with the support of third-party cybersecurity experts.
Okta says hackers stole data for all customer support users in cyber breach
The San Francisco-based company notified customers that it has determined hackers downloaded a report containing data including names and email addresses of all clients that use its customer support system, the company said in an emailed statement to Reuters.
Vulnerability
Our attack surface.
CVE-2023-4193: strongSwan Vulnerability
A vulnerability in charon-tkm related to processing DH public values was discovered in strongSwan that can result in a buffer overflow and potentially remote code execution. All versions since 5.3.0 are affected.
https://www.strongswan.org//blog/2023/11/20/strongswan-vulnerability-(cve-2023-41913).html
GnuTLS: timing sidechannel in RSA-PSK key exchange
A vulnerability was found that the response times to malformed ciphertexts in RSA-PSK ClientKeyExchange differ from response times of ciphertexts with correct PKCS#1 v1.5 padding. Only TLS ciphertext processing is affected
https://gnutls.org/security-new.html#GNUTLS-SA-2023-10-23
The Internet of Insecure Cows
Agritech risk is going to be one of those areas where cyber and food security crash together. Samuel Barnes-Thornton, Joseph Gardine and Awais Rashid open the door through which we can expect much more research to flow from.
This is the first practical cyber security analysis of such devices that are currently in use on farms. We have successfully reverse-engineered the wireless protocol and demonstrated the ability to inject false data into the system, posing as one of the sensors. Testing has shown that both the system to receive signals from the sensors and the data endpoint software are vulnerable to data injection. This paper highlights the specific threats from the vulnerabilities and identifies potential countermeasures that could be integrated into the sensors in the future.
https://dl.acm.org/doi/10.1145/3605758.3623498
Offense
Attack capability, techniques and trade-craft.
Fun with another PatchGuard-compliant Hook
Aidan Khoury and, Daax Rynd show there is still plenty of value to be had from low level windows research. Subverting PatchGuard in this way to have kernel hooks gets the world back to something once possible on older platforms.
This uses similar mechanics, and was derived from continued research within the ETW functions of the Windows Kernel. This method has been tested from early Windows 10 to latest Windows 11 23h2. The hook allows for a number of different, useful hooks. We’ll take a look at the most interesting one, in my opinion, for anti-malware/anti-cheat purposes.
https://revers.engineering/fun-with-pg-compliant-hook/
Process Injection - Avoiding Kernel Triggered Memory Scans
Fabian Mosch shares some tradecraft which will cause some EDRs pain..
But most vendors (for good reasons) tend to verify known malicious before preventing execution via memory scans. By hiding the known malicious at the time of the execute primitive it’s therefore enough to still get a known malicious implant to run via Process Injection. The Proof of Concept Caro-Kann demonstrates that by injecting a second custom shellcode, which sleeps, decrypts the known malicious on runtime and jumps to it.
https://www.r-tec.net/r-tec-blog-process-injection-avoiding-kernel-triggered-memory-scans.html
GhostMapper
Oliver details a novel technique for Windows.
When a crash occurs some drivers that need to save data to the disk may be the drivers that caused the crash, therefore we have a replica of those drivers with the dump_ prefix with the original driver being without the prefix. If we want to save important data to the disk before a crash the ghost drivers can be activated and used. The ghost drivers are monitored and managed by the crashdmp.sys driver and in that driver are some interesting information that I will take up later. In reality, the ghost driver is rarely used but could be abused and modified to anyone's liking.
https://github.com/Oliver-1-1/GhostMapper
Hypothesis: longer passwords tend to contain a few (or just one) character(s) that would be outlier(s) within a trigram
Applying statistics to password cracking strategies.
Hypothesis: longer passwords tend to contain a few (or just one) character(s) that would be outlier(s) within a trigram. In other words, what's statistically unlikely among 3 characters becomes statistically likely to appear at least once (or perhaps exactly once) among, say, 8 characters. (A related hypothesis, not to be tested here, is that the same holds true for words in a passphrase.) I use a representative 1 million non-unique NT hash sample from HIBP v8 generated using my pwned-passwords-sampler (which virtually repeats each hash according to its count, then takes a random sample). There are 826973 unique hashes in the sample.
https://www.openwall.com/lists/john-users/2023/11/25/1
Exploitation
What is being exploited.
Exploitation of Unitronics PLCs used in Water and Wastewater Systems
Reporting from CISA on this active exploitation of PLCs used in Water treatment.
CISA is responding to active exploitation of Unitronics programmable logic controllers (PLCs) used in the Water and Wastewater Systems (WWS) Sector. Cyber threat actors are targeting PLCs associated with WWS facilities, including an identified Unitronics PLC, at a U.S. water facility. In response, the affected municipality’s water authority immediately took the system offline and switched to manual operations—there is no known risk to the municipality’s drinking water or water supply.
Further reporting from the Water-ISAC
according to open-source reporting, on Saturday the Municipal Water Authority of Aliquippa in western Pennsylvania was attacked by an Iranian-backed cyber group known as CyberAv3ngers.
GoTitan Botnet - Ongoing Exploitation on Apache ActiveMQ
Further example of a botnet being building through an n-day.
The attacker initiates a connection to ActiveMQ through the OpenWire protocol, typically on port 61616. By transmitting a crafted packet, the attacker triggers the system to unmarshal a class under their control. This action, in turn, prompts the vulnerable server to retrieve and load a class configuration XML file from a specified remote URL, requiring the presence of a predefined XML file hosted externally.
https://www.fortinet.com/blog/threat-research/gotitan-botnet-exploitation-on-apache-activemq
Tooling and Techniques
Low level tooling and techniques for attack and defence researchers…
Intercepting Windows memory allocations
Sina Karvandi provides a valuable work aid.
gist.github.com/SinaKarvandi/f3c037f3bde210c7f1e606606db9bd99
Footnotes
Some other small (and not so small) bits and bobs which might be of interest.
Aggregate reporting
ANSSI Presentation - on incidents in french.
Geopolitical Cyber Risk: Going Beyond the Industry and Region
Chromium Money Tree Browser - where money has been earnt finding vulnerabilities
Tmp.out #3 - old school esq zine.
Artificial intelligence
GPT is becoming a Turing machine: Here are some ways to program it
Can Q-Learning with Graph Networks Learn a Generalizable Branching Heuristic for a SAT Solver?
A* Search Without Expansions: Learning Heuristic Functions with Deep Q-Networks
White-Box Transformers via Sparse Rate Reduction: Compression Is All There Is?
Books
None this week
Events
Unless stated otherwise, linked or referenced content does not necessarily represent the views of the NCSC and reference to third parties or content on their websites should not be taken as endorsement of any kind by the NCSC. The NCSC has no control over the content of third party websites and consequently accepts no responsibility for your use of them.
This newsletter is subject to the NCSC website terms and conditions which can be found at https://www.ncsc.gov.uk/section/about-this-website/terms-and-conditions and you can find out more about how will treat your personal information in our privacy notice at https://www.ncsc.gov.uk/section/about-this-website/privacy-statement.




Ollie- BHEUR Keynote...awesome sauce m8! I'm sorry I won't be there to hear it...but I hope you knock it out of the park!
Another excellent post Ollie, thanks. Have we heard anything about similar attacks to that sustained by NXP here in the U.K.?