CTO at NCSC Summary: week ending August 24th
"Across June and July 2025, the AI Incident Database added over sixty new incident IDs"
Welcome to the weekly highlights and analysis of the blueteamsec Lemmy (and my wider reading). Not everything makes it in, but the best bits do.
Operationally this week nothing overly of note…
In the high-level this week:
North Korea accused of £17m crypto heist that killed British start-up - The Telegraph reports - “Lykke was founded in 2015 and operated from Switzerland but was registered in the UK. The company said last year that it had lost $22.8m (£16.8m) in Bitcoin, Ethereum and other cryptocurrencies, forcing it to halt operations.” … “North Korea was named as the potential hacker in a recent report by the Office of Financial Sanctions Implementation (OFSI), a branch of the Treasury.”
Crypto Assets Threat Assessment - The Office of Financial Sanctions Implementation in the UK publishes - “It is highly likely that UK-based cryptoasset firms are currently at risk of being targeted by DPRK-linked hackers and IT workers seeking to steal or obtain funds through illicit means.”
Scam Farms Marque and Reprisal Authorization Act of 2025 - Rep. David Schweikert submits to congress - “To authorize the President of the United States to issue letters of marque and reprisal with respect to acts of aggression against the United States a member of a criminal enterprise or any conspirator associated with an enterprise involved in cybercrimes, and for other purposes.”
Russian hackers seized control of Norwegian dam, spy chief says - The Guardian reports - “Russian hackers took control of a Norwegian dam this year, opening a floodgate and allowing water to flow unnoticed for four hours, Norway’s intelligence service has said.” - happened in April now just being attributed by Norwegian intelligence
Tackling the National Gap in Software Understanding - CISA, DARPA, OUSD R&E, NSA, and National Nuclear Security Agency call to shape research priorities - “We invite software analysis experts and mission owners to engage with CISA and our partners at DARPA, OUSD R&E, NSA, and National Nuclear Security Agency as we collectively shape research priorities and maintain a sustained focus on addressing this critical challenge.”
Hacking and Firewalls Under Siege: Russia’s Cyber Industry During the War on Ukraine - CNA publishes - “Some of these firms (and others not covered in this paper) are directly supporting the Russian government’s offensive cyber operations, making them direct security risks for the United States and the West.”
Improving Private Sector Cyber Victim Notification and Support - Institute for Security and Technology publish - “The report concludes with three main recommendations for cloud service providers (CSPs) and other stakeholders:
Improve existing notification processes and develop best practices for industry.
Support the development of “middleware” necessary to share notifications with victims privately, securely, and across multiple platforms including through native notifications.
Improve support for victims following notification.”
Tchap: Secure messaging mandatory in the public sphere from September 1 - French Prime Minister directs - “To ensure the security of conversations and information shared via instant messaging, it is recommended that TCHAP instant messaging be widely deployed.”
Big ‘Make in India’ push! Cabinet approves four new semiconductor projects; cumulative investment of around Rs 4,600 crore eyed - The Times of India reports - “The approval of these projects will substantially strengthen the country's semiconductor ecosystem, featuring the nation's first commercial compound fabrication facility and an advanced glass-based substrate semiconductor packaging unit.”
Reporting on/from China
Analysis of the GFW's Unconditional Port 443 Block on August 20, 2025 - GFW Report publishes - “Between approximately 00:34 and 01:48 (Beijing Time, UTC+8) on August 20, 2025, the Great Firewall of China (GFW) exhibited anomalous behavior by unconditionally injecting forged TCP
RST+ACKpackets to disrupt all connections on TCP port 443. This incident caused massive disruption of the Internet connections between China and the rest of the world”Chinese cyber theft car drivers with mobile network transmitters touring Bangkok arrested by police - Thai Examiner reports - “The Chinese handler reportedly mailed him a full kit: a battery, base station, antenna, router, and setup instructions. He also sent a ฿2,000 deposit to secure the deal. Then, he trained Nopparat remotely and gave him orders to drive around and transmit fake messages. "Initially, Nopparat used his personal car. He was paid between ฿3,300 and ฿3,500 per day. He sent between 5,000 and 10,000 phishing messages daily. These texts mimicked official messages from banks, e-commerce sites, and government agencies.”
China’s Tsinghua University helps to break 40-year-old maths cap on computer speed - South China Morning Post reports - “The new algorithm first splits the graph into layers, grouping neighbouring nodes within a certain range, or “frontier”. It then uses the Bellman-Ford algorithm to identify influential frontier nodes and only performs detailed calculations on key nodes, thereby significantly reducing computational complexity.”
China’s mega dam Xiluodu stops using Western industrial chips over security concerns - South China Morning Post reports - “had replaced long-standing foreign “programmable logic controllers” (PLCs) – from German giant Siemens and French firm Schneider Electric – with a domestically developed system powered by fully home-grown Loongson 3C6000 processors.”
Tencent says it has ample chips for AI training amid reported purchase halt - Nikkei Asia reports - "But from our own perspective, we do have enough chips for training and continuous upgrade of our existing models," he said, "and we also have many options for inference chips, and we are also executing a lot of software improvement and upgrade in order to drive efficiency gain in inference so that we can actually put more workload on the same number of chips."
Huawei unveils algorithm that could cut China’s reliance on foreign memory chips - South China Morning Post reports - “Unified Cache Manager (UCM) is an algorithm that allocates data according to varying latency requirements across different types of memories – including ultra-fast HBM, standard dynamic random access memory and solid-state drive – thereby enhancing inference efficiency, according to Huawei executives at the Financial AI Reasoning Application Landing and Development Forum in Shanghai on Tuesday.”
AI
AIxCC Open Source Archive - DARPA and ARPA-H curate - “all 7 finalist teams are releasing their competition Cyber Reasoning Systems (CRSs) open-source in order to accelerate the distribution and use of the AIxCC-developed technology within the cybersecurity and software development fields.”
AI Incident Roundup – June and July 2025 - The AI Incident Database summarises- “Across June and July 2025, the AI Incident Database added over sixty new incident IDs. These entries capture a range of harms, from sophisticated state-directed campaigns to opportunistic fraud and platform-level failures.”
Design Principles for LLM-based Systems with Zero Trust - Federal Office for Information Security (BSI) and ANSSI release - “The following design principles for secure LLM systems enhance resilience against attacks and unintended errors, forming the foundation for trustworthy LLM systems. They aim to structure interactions between system components in a way that minimizes risks such as misuse, data exfiltration, and system malfunctions, while ensuring functionality and user-friendliness. The overarching objective is to minimize the risks of Poisoning, Evasion and Privacy Attacks. “
THOR: Secure Transformer Inference with Homomorphic Encryption - Hanyang University, Yonsei University and University of Texas publish - “Our matrix multiplication algorithms reduce the number of key-switching operations in the linear layers of the attention block in the BERT-base model by up to 14.5x, compared to the state-of-the-art HE-based secure inference protocol (Park et al., Preprint). Combined with cryptographic optimizations, our experimental results demonstrate that THOR provides secure inference for the BERT-base model with a latency of 10.43 minutes on a single GPU, while maintaining comparable inference accuracy on the MRPC dataset.” - reminder we published guidance as NCSC in April on Deciding when to use Advanced Cryptography to protect your data
Scamlexity - Guard.io research - “AI Browsers promise a future where an Agentic AI working for you fully automates your online tasks, from shopping to handling emails. Yet, our research shows that this convenience comes with a cost: security guardrails were missing or inconsistent, leaving the AI free to interact with phishing pages, fake shops, and even hidden malicious prompts, all without the human’s awareness or ability to intervene.”
MCP vulnerability case study: SQL injection in the Postgres MCP server - Datadog Security Labs research - “Users should avoid using the now deprecated Postgres MCP server when connecting to any database where write operations should be prevented. In particular, they should avoid using it in production use cases.” - new AI integrations managing with 25 year old vulnerability classes and highlighting the importance of the UK’s AI Code of Practice which builds on the Software Code of Practice.
All You Need Is MCP - LLMs Solving a DEF CON CTF Finals Challenge - Wil Gibbs publishes - “This was mind-blowing—so much so, in fact, that literally every person in our suite did not believe me and thought the code was somehow misrepresentative of the output… But no. It got the flag.”
Seizing the agentic AI advantage - McKinsey publish - “But unlocking the full potential of agentic AI requires more than plugging agents into existing workflows. It calls for reimagining those workflows from the ground up—with agents at the core.”
How China seeks to distribute AI while US only wants to dominate - South China Morning Post opines - “The result is that China’s models and agents are proliferating, embedded in workflows from logistics to finance. For the Global South, they offer affordability, localisation and deployment freedom. In many ways, China is treating AI the way it once treated high-speed rail or 5G: as national infrastructure with export potential. This strategic framing boosts adoption, soft power and standard-setting, all without needing to bother with the West.”
Cyber proliferation
How a Czech Supply Chain Feeds the Global Spyware Machine - VSquare disclose - “Several people living in the Czech Republic have worked for Intellexa, the spyware company, representatives of which have been accused of assisting with human rights violations and are currently on trial in Greece. Investigace.cz has obtained more documents that show an in-depth picture of the involvement of these actors. Central to Intellexa’s operations is Dvir Horef Hazan, an Israeli entrepreneur living in a small Silesian town. Investigace.cz visited the center of operations in Krnov, which, featuring a large Israeli flag draped on the outside, resembles an embassy.”
Advance Security Solutions offers $20millio for SMS/MMS 0day and $15 million for iOS chains - amongst other platforms - from the Middle East
Bounty Hunting
Serial hacker who defaced official websites is sentenced - UK National Crime Agency announce - “Forensic analysis of his laptop and several mobile phones showed that Al-Mashriky had infiltrated a number of websites including the Yemen Ministry of Foreign Affairs, the Yemen Ministry of Security Media and an Israeli news outlet.”
Oregon man charged with administering “Rapper Bot” DDoS-for-hire Botnet - US Department of Justice announces - “Rapper Bot, aka “Eleven Eleven Botnet” and “CowBot,” is a Botnet that primarily compromises devices like Digital Video Recorders (DVRS) or WiFi routers at scale by infecting those devices with specialized malware. Clients of Rapper Bot then issue commands to those infected victim devices, forcing them to send large volumes of “Distributed Denial of Service” (DDoS) traffic to different victim computers and servers located throughout the world.”
Palm Coast Hacker Sentenced To 10 Years In Prison - US Department of Justice announces - “Noah Michael Urban (20, Palm Coast), a/k/a “King Bob,” “Sosa,” “Elijah,” and “Gustavo Fring,” to 10 years in federal prison for conspiracy to commit wire fraud, wire fraud, and aggravated identity theft. The court also ordered Urban to forfeit approximately $4.8 million in assets, which includes cryptocurrency and other property. Urban was also ordered to pay $13 million in restitution. Urban entered a guilty plea on April 4, 2025.”
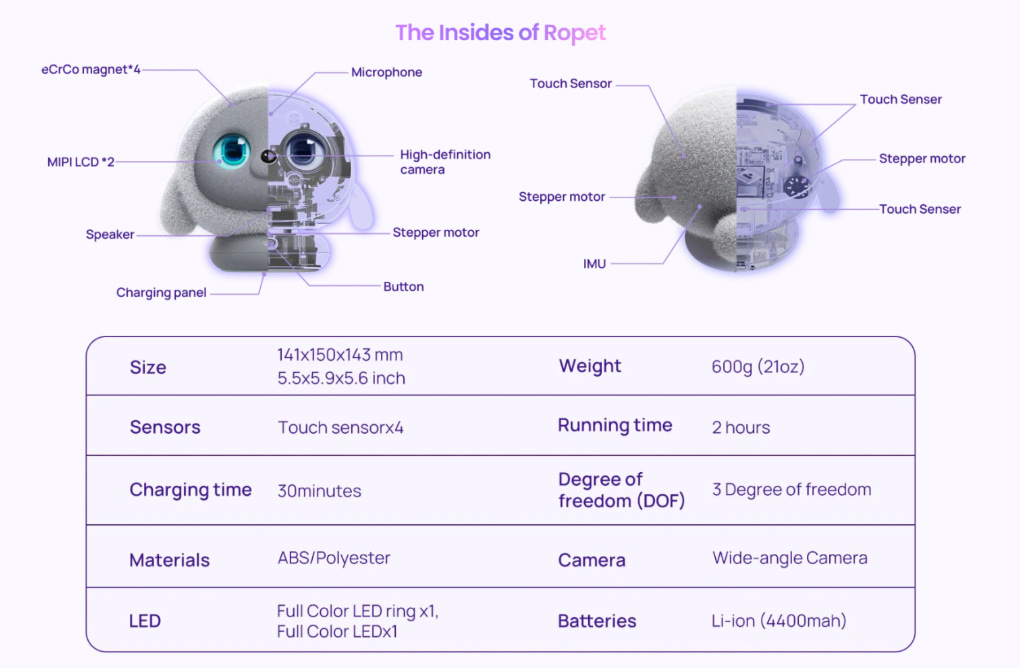
Reflections this week build on those from the week ending August 10th around robotics and resilient platforms. If you have not clocked what is happening have a look at these two families out of China in the last 4 weeks:
They are developing quickly, converging with AI and employing the competition model to accelerate development - in this instance in the guise of World Humanoid Games.
At the other end meet Ropet by RopiAI also out of China who outlines its value as:
“In a world that feels increasingly disconnected, Ropet was born with a quiet mission—to ease your loneliness and help you rediscover what it means to love and be loved.”
Edge AI to tell feelings and thoughts to …
To reiterate .. if we do not look to ensure these solutions are built employing secure by design and specifically:
Platform integrity and attestation e.g. what the Trust Computing Group provide
Immutable identity based on cryptographic primitives
Observability to detect breaches
Transparency in technology
Memory safety e.g. CHERI, Rust, Go and similar
.. and more
Then we should not be surprised by the outcome and the very real world implications which will stem from poor cyber resilience in these systems..
Not getting this via email? Subscribe:
Think someone else would benefit? Share:
All attribution is by others and not the UK Government unless specifically stated as such, please see the legal text at the end.
Have a lovely Friday…
Ollie
Cyber threat intelligence
Who is doing what to whom and how allegedly.
Reporting on Russia
Russian Government Cyber Actors Targeting Networking Devices, Critical Infrastructure
FBI details and attributes this alleged Russian state campaign against networking equipment. Patch and ensure secure configurations..
The Federal Bureau of Investigation (FBI) is warning the public, private sector, and international community of the threat posed to computer networks and critical infrastructure by cyber actors attributed to the Russian Federal Security Service's (FSB) Center 16. The FBI detected Russian FSB cyber actors exploiting Simple Network Management Protocol (SNMP) and end-of-life networking devices running an unpatched vulnerability (CVE-2018-0171) in Cisco Smart Install (SMI) to broadly target entities in the United States and globally.
In the past year, the FBI detected the actors collecting configuration files for thousands of networking devices associated with US entities across critical infrastructure sectors. On some vulnerable devices, the actors modified configuration files to enable unauthorized access to those devices. The actors used the unauthorized access to conduct reconnaissance in the victim networks, which revealed their interest in protocols and applications commonly associated with industrial control systems.
The FSB Center 16 unit conducting this activity is known to cybersecurity professionals by several names, including "Berserk Bear" and "Dragonfly," which refer to separate but related cyber activity clusters. For over a decade, this unit has compromised networking devices globally, particularly devices accepting legacy unencrypted protocols like SMI and SNMP versions 1 and 2. This unit has also deployed custom tools to certain Cisco devices, such as the malware publicly identified as "SYNful Knock" in 2015.
https://www.ic3.gov/PSA/2025/PSA250820
Sara McBroom and Brandon White also report on the same campaign from a Cisco perspective:
Static Tundra is a Russian state-sponsored cyber espionage group linked to the FSB's Center 16 unit that has been operating for over a decade, specializing in compromising network devices for long-term intelligence gathering operations.
The group actively exploits a seven-year-old vulnerability (CVE-2018-0171), which was patched at the time of the vulnerability publications, in Cisco IOS software's Smart Install feature, targeting unpatched and end-of-life network devices to steal configuration data and establish persistent access.
Primary targets include organizations in telecommunications, higher education and manufacturing sectors across North America, Asia, Africa and Europe, with victims selected based on their strategic interest to the Russian government.
Static Tundra employs sophisticated persistence techniques including the historic SYNful Knock firmware implant (first reported in 2015) and bespoke SNMP tooling to maintain undetected access for multiple years.
The threat extends beyond Russia's operations — other state-sponsored actors are likely conducting similar network device compromise campaigns, making comprehensive patching and security hardening critical for all organizations.
Threat actors will continue to abuse devices which remain unpatched and have Smart Install enabled.
https://blog.talosintelligence.com/static-tundra/
UAC-0057 keeps applying pressure on Ukraine and Poland
Harfang Lab detail this alleged Russian campaign which is only of note due to the regional targeting.
We identified a cluster of compressed archive files which were likely intended to be delivered to Ukrainian targets between late May 2025 and late July 2025. We could not determine how those archives were delivered, but we believe they were distributed via spearphishing emails, either as attachments or through download links.
These archives contain XLS spreadsheets with a VBA macro that drops and loads a DLL. The latter is responsible for collecting information about the compromised system and retrieving next stage malware from a command and control (C2) server.
https://harfanglab.io/insidethelab/uac-0057-pressure-ukraine-poland/
Reporting on China
MURKY PANDA: A Trusted-Relationship Threat in the Cloud
CrowdStrike detail this alleged Chinese operation which is noteworthy for both the technical capability on show but also the level of activity. Also a lesson in why timely patching is a super power.
Since late 2024, CrowdStrike Counter Adversary Operations has observed significant activity conducted by MURKY PANDA, a China-nexus adversary that has targeted government, technology, academic, legal, and professional services entities in North America.
MURKY PANDA has previously conducted trusted-relationship compromises in the cloud and demonstrates extensive knowledge of cloud environments and custom application logics.
The adversary has also shown considerable ability to quickly weaponize n-day and zero-day vulnerabilities and frequently achieves initial access to their targets by exploiting internet-facing appliances.
MURKY PANDA has deployed web shells including Neo-reGeorg during their cyberespionage operations and has access to a low-prevalence malware family tracked by CrowdStrike Counter Adversary Operations as CloudedHope.
MURKY PANDA operations are likely driven by intelligence-collection objectives to gain access to sensitive information. The adversary has previously exfiltrated emails and other sensitive documents from high-profile targets.
MURKY PANDA heavily relies on exploiting internet-facing appliances to gain initial access and has frequently deployed web shells — including the Neo-reGeorg web shell frequently used by China-nexus adversaries — to establish persistence. The adversary also has access to the low-prevalence custom malware family CloudedHope.
https://www.crowdstrike.com/en-us/blog/murky-panda-trusted-relationship-threat-in-cloud/
Reporting on North Korea
Unmasking the DPRK-linked GitHub C2 Espionage Campaign
Pham Duy Phuc and Alex Lanstein detail an alleged North Korean operation which is noteworthy due to the victimology. The tradecraft is rather repetitive and well understood.
Initial vector – spear-phishing: The campaign’s entry point was a wave of spear-phishing emails sent to personnel at embassies and foreign ministries in Seoul. These emails were carefully crafted to appear legitimate, often spoofing real diplomats or officials. For instance, one lure email impersonated a First Secretary of an EU delegation, offering “EU political counselors meeting minutes” as an attachment. Another, sent on May 19, 2025, posed as a protocol officer from the U.S. Embassy, inviting recipients to an Independence Day event. Common across all emails was the inclusion of a ZIP file (indicated by documents like “Attachment: Invitation...zip; Password: USProtocol”). Inside each ZIP was a Windows shortcut with double extension (pdf.lnk) file disguised with a PDF icon and name (e.g., "Urgent Letter from the Ambassador.pdf.lnk").
https://www.trellix.com/blogs/research/dprk-linked-github-c2-espionage-campaign/
LazarOps: APT Tactics Targeting the Developers Supply Chain
Security Joes provides summary analysis of a set of campaigns which are allegedly North Korean in origination and we know have been running for some time. Noteworthy as developer environments often have less controls coupled with the ability to do achieve production environment access.
From attacker infrastructure to token reuse, the campaign left behind several forensic fingerprints:
Shared infrastructure: Domains like fashdefi[.]store and bujey[.]store were used across all repositories
Port behavior: Use of port 1224 for HTTP fetches and port 6168 for malware delivery
Token reuse: Identical MongoDB strings and API keys were embedded across multiple payloads
Disposable identities: Most commits came from accounts that were either newly created or later deleted
Victim themes: Projects focused on AI, NFT, AR fashion, and crypto-backed platforms
Recruitment lure scale: LinkedIn messages and InMails suggested that over 200 developers were targeted across EMEA and APAC regions
https://www.securityjoes.com/post/operation-lazarops-over-50-github-accounts-tied-to-lazarus-fake
Detailed Analysis of Phrack’s APT Down: The North Korea Files
S2W analyze the data leak from this alleged North Korean group of actors - noteworthy as it further underlines some previous observations about an alleged link/association with another country.
Examination of the leaked dataset suggests the actor operated in a Chinese-language environment.
The actor made extensive use of Chinese platforms such as Baidu (search engine), CSDN and Freebuf (cybersecurity blogs), AcFun and Bilibili (video streaming platforms) without translation, while relying on Google Translate to convert non-Chinese languages into Simplified Chinese.
The use of Baidu Cloud was confirmed. This service requires verified identity documents such as a Chinese national ID or passport, suggesting access to an authenticated Chinese account.
Source code comments and personal documents within the dataset were also authored in Chinese.
https://s2w.inc/en/resource/detail/908
StardustChollima/BlueNoroff stole TG accounts and launched ZoomClickFIX phishing attacks
Reporting out of China on this alleged North Korean campaign from earlier in the month which I had missed. Noteworthy due to the objective..
Recently, StardustChollima/BlueNoroff was caught stealing a legitimate user's TG account and launching a ZoomClickFIX phishing attack.
Therefore, this operation is attributed to StardustChollima/BlueNoroff. It is mainly an attack against individuals in the industry with the purpose of stealing money, not an attack against traders and companies. However, this group has some overlap in behavior and actions with TraderTraitor/LabyrinthChollima/unc4899. Both are branches of APT38 and are very powerful. Compared with the active FamousChollima, they are far more powerful.
https://mp.weixin.qq.com/s/r1FAt-vHn-Yuw2wu54s5Rg
Reporting on Iran
APT MuddyWater Targets CFOs with Multi-Stage Phishing & NetBird Abuse
Hunt.io detail more alleged North Korean activity which aligns with well understood tradecraft. Noteworthy for the misuse of legitimate remote monitoring solutions..
Initial Access: Social engineering via spear-phishing emails leading to Firebase-hosted phishing pages with math-based CAPTCHA lures.
Payload Delivery: Multi-stage infection using VBS downloaders, ZIP archives, and secondary payloads delivered from attacker-controlled infrastructure.
Persistence Mechanisms: Deployment of NetBird and OpenSSH, creation of hidden local admin accounts, enabling RDP, and scheduled task automation.
Infrastructure Evolution: Shift from 192.3.95.152 to 198.46.178.135; multiple hosting paths (/job/ vs /scan/) within the same Firebase/Web App projects.
Attribution: Overlaps in infrastructure, TTPs, and tools with known APT MuddyWater campaigns.
Pivot Discoveries: Identification of multiple related Firebase/Web App domains using identical phishing kits and AES-encrypted redirect logic.
Legitimate Tool Abuse: Misuse of NetBird and AteraAgent.exe for remote access and monitoring.
https://hunt.io/blog/apt-muddywater-deploys-multi-stage-phishing-to-target-cfos
Reporting on Other Actors
Detailed Analysis of the Stealer-Traffer Ecosystem
S2W details how the ecosystem behind stealers works in part, noteworthy due to the focus on SEO techniques.
The Stealer ecosystem consists of Stealer developers (Stealer Operators), Traffic Team administrators, and Traffers who operate within the Traffic Team.
The Traffic Team is an organized group that distributes Stealer malware, sells logs from infected systems, and generates revenue. It is composed of Traffers and Traffic Team administrators, with additional roles such as technical specialists or settlement managers, depending on the team.
A Traffer refers to an attacker operating within the Traffic Team in the Stealer ecosystem, aiming to increase the number of infected users through activities such as cryptocurrency theft, distribution of phishing panels, and dissemination of malicious ads.
Job postings for Traffers or promotional posts for the Traffic Team are primarily uploaded on Russian-language forums. Interested Traffers contact the team directly through Telegram Bot links provided in the posts to join the team.
The forum with the highest activity related to Traffer posts is the XSS forum, with a total of 8,733 posts uploaded during the analysis period (January 2018 to August 2025).
Traffers use various methods to distribute malware and utilize search engine optimization (SEO) to direct large amounts of traffic to malicious sites.
SEO generally refers to techniques used to manipulate search engines such as Google, Yandex, and Bing so that a website or page appears at the top of search results for specific keywords. However, traffers active in Traffic Teams exploit this technique to redirect users to malicious links or phishing pages.
The xemplex SEO Team active on the Lolz Guru forum uses SEO through CTR manipulation, automatic link farm construction, and methods to evade Panda and Penguin algorithms.
The target operating systems (OS) and browser environments targeted by the Traffic Team vary depending on the type of Stealer malware used by the organization, and some Traffic Teams also list the information stealers they use.
An analysis of the promotional posts by the Dungeon Team, a Traffic Team active on the Lolz Guru forum, reveals the operational methods of Traffic Teams.
When a Traffer joins a Traffic Team, they are provided with a FUD Loader, a custom crypter specifically for stealers, and free SEO services. Profits are distributed between the Traffer and the administrator in a 65:35 ratio.
- There are cases where cryptocurrency miners are hidden within the Stealer Loader.
https://medium.com/s2wblog/detailed-analysis-of-the-stealer-traffer-ecosystem-40ba805e1bca
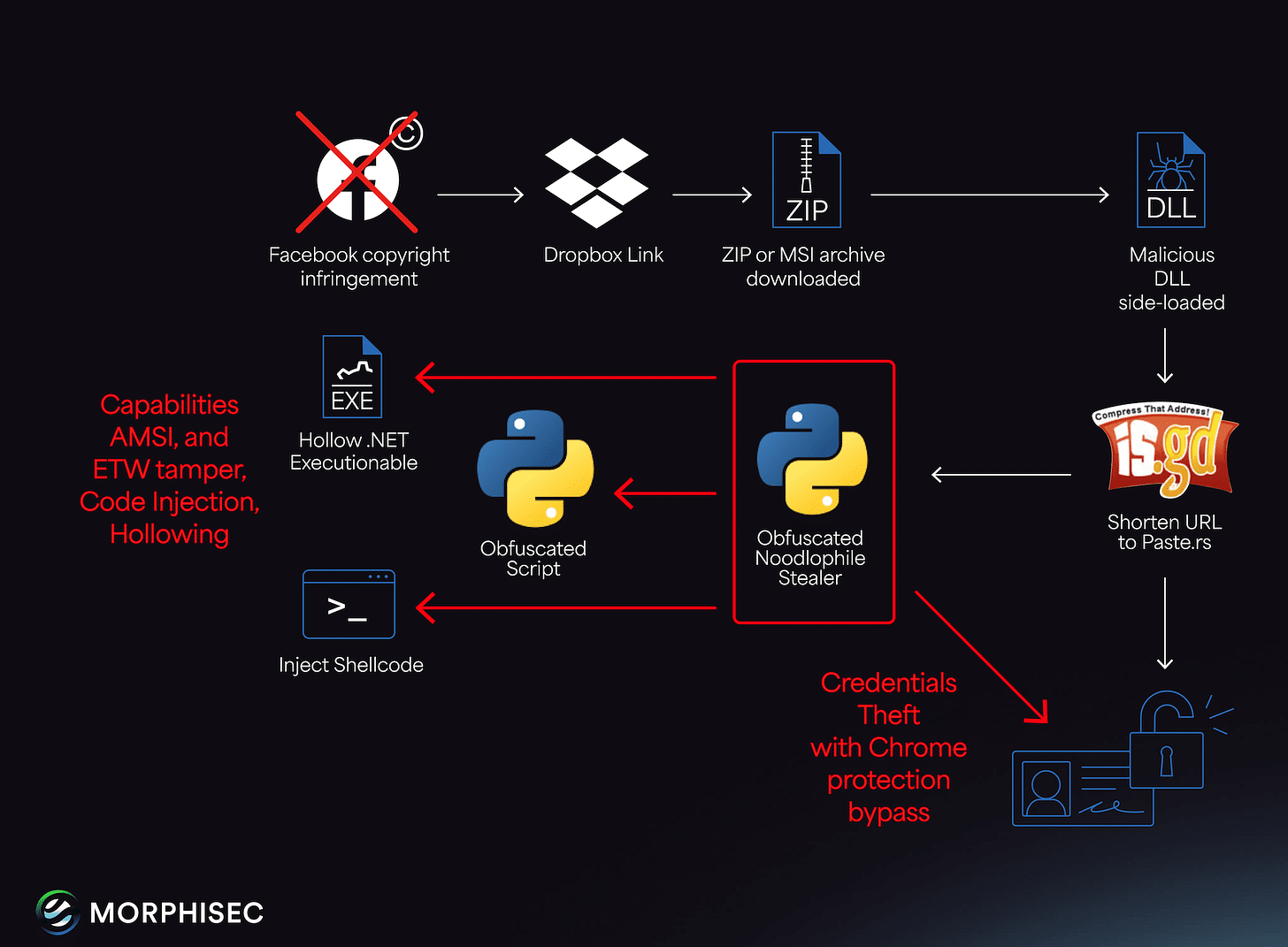
Noodlophile Stealer Evolves: Targeted Copyright Phishing Hits Enterprises with Social Media Footprints
Shmuel Uzan details a criminal campaign which uses novel as opposed to sophisticated phishing emails. Noteworthy due to the individuals who would likely receive and then likely be compelled to investigate / interact with the lures.
The Noodlophile campaign, active for over a year, now leverages advanced spear-phishing emails posing as copyright infringement notices, tailored with reconnaissance-derived details like specific Facebook Page IDs and company ownership information. Unlike its earlier iteration, which used fake AI video generation platforms, this campaign employs multilingual lures (potentially AI-crafted), broader global outreach, and upgraded delivery mechanisms to deploy an enhanced Noodlophile Stealer.
Cybercriminals Abuse AI Website Creation App For Phishing
Tommy Madjar and Selena Larson detail a campaign which is noteworthy due to the use of an AI platform to scale their activity. Easy to mitigate but annoying..
Threat actors are increasingly using an AI website generation platform to create fraudulent websites for credential phishing and malware delivery.
Threat actors created or cloned websites that impersonated prominent brands, used CAPTCHA for filtering, and posted credentials to Telegram.
Cybercriminals are increasingly using an AI-generated website builder called Lovable to create and host credential phishing, malware, and fraud websites.
'Blue Locker' Analysis: Ransomware Targeting Oil & Gas Sector in Pakistan
Resecurity summarises a National Computer Emergency Response Team (CERT) of Pakistan advisory regarding ransomware. Noteworthy due to the regional targeting .
The National Computer Emergency Response Team (CERT) of Pakistan has recently issued warnings to 39 ministries regarding the threat posed by "Blue Locker" ransomware. This alert underscores the seriousness of the threat, highlighting the potential for significant data loss and operational disruption within governmental organizations.
The advisory places organizations in Pakistan on high alert, indicating that "Blue Locker" is actively targeting critical infrastructure and government bodies in the country. This reflects a broader trend of increasing ransomware attacks globally, with Pakistan now being a specific target for such campaigns.
Notably, NCERT connected the "Blue Locker" ransomware with the "Shinra" malware family, which, according to their advisory, shares similarities with Conti and Black Basta
Discovery
How we find and understand the latent compromises within our environments.
FACADE: Fast and Accurate Contextual Anomaly DEtection
Google release this which will provide edge to a number of organisations who are mature enough to take it and the concepts forward.
FACADE is an enterprise-security anomaly detection system developed by Google. It is a high-precision deep-learning-based machine learning system used in a number of applications across Google. It is used as a last line of defense against insider threats, as an ACL recommendation system, and as a way to detect account compromise.
It is built around a new multi-modal model that is trained on corporate document access, SQL query, and HTTP/RPC request logs.
https://github.com/google/facade
Defence
How we proactively defend our environments.
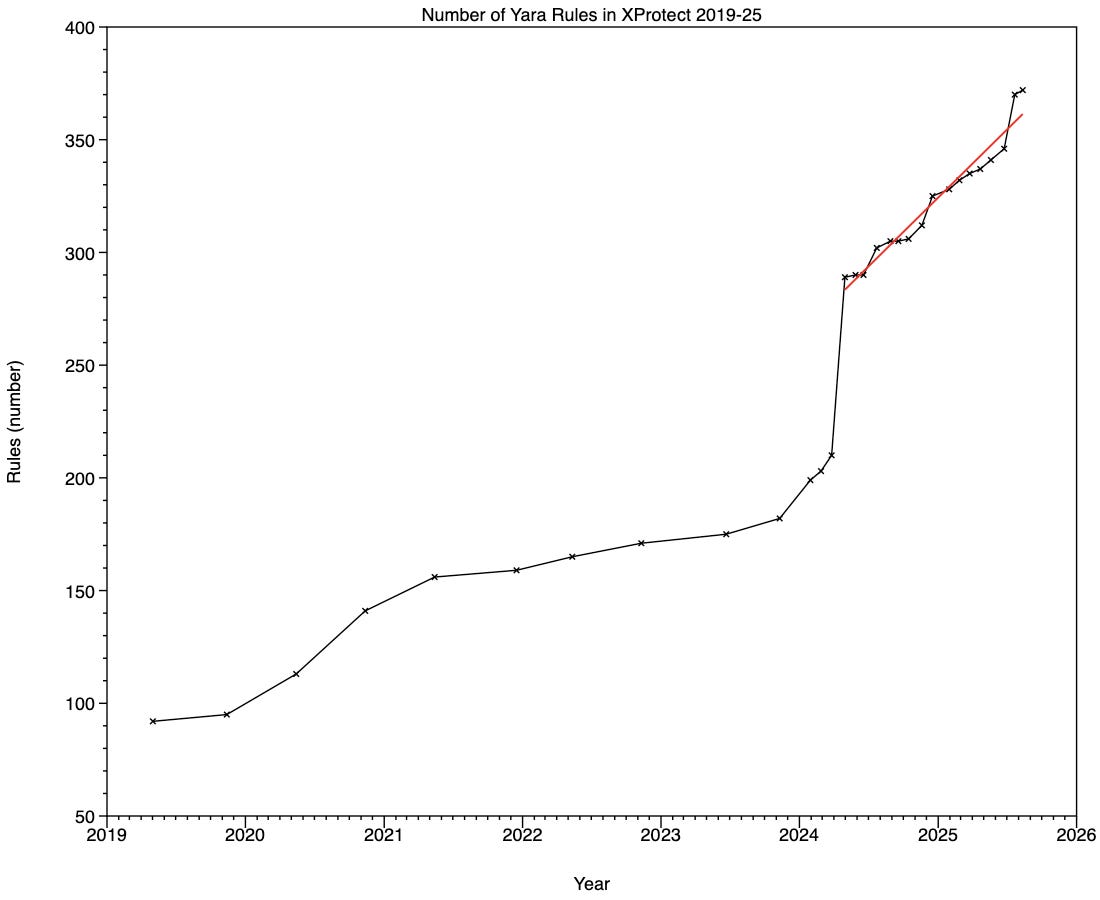
How XProtect’s detection rules have changed 2019-25
An analysis of how Apple’s malware detection rules have grown over time..
In late 2024, XProtect in macOS Sequoia started using iCloud to deliver its XProtect data updates. For this analysis I have excluded version 5273, which was only released via iCloud and wasn’t provided through the regular
softwareupdateroute used by all previous versions.
https://eclecticlight.co/2025/08/15/how-xprotects-detection-rules-have-changed-2019-25/
AppLocker Inspector
Spencer Alessi releases a tool which is both useful an co-developed with an LLM
AppLocker Inspector audits an AppLocker policy XML and reports weak/misconfigured/risky settings, including actual ACL checks. If you don’t provide a policy file, the tool will export the local effective AppLocker policy and analyze that automatically.
https://github.com/techspence/AppLockerInspector
There and Back Again: Detecting OT devices across protocol gateways
Incident Writeups & Disclosures
How they got in and what they did.
Protecting You From Social Engineering Campaigns: An Update From Workday
Workday detail their CRM breach which a number of organisations have experienced and disclosed recently.
In this campaign, threat actors contact employees by text or phone pretending to be from human resources or IT. Their goal is to trick employees into giving up account access or their personal information.
We recently identified that Workday had been targeted and threat actors were able to access some information from our third-party CRM platform. There is no indication of access to customer tenants or the data within them. We acted quickly to cut the access and have added extra safeguards to protect against similar incidents in the future.
The type of information the actor obtained was primarily commonly available business contact information, like names, email addresses, and phone numbers, potentially to further their social engineering scams.
Vulnerability
Our attack surface.
Conflicting Scores, Confusing Signals: An Empirical Study of Vulnerability Scoring Systems
Viktoria Koscinski, Mark Nelson, Ahmet Okutan, Robert Falso and Mehdi Mirakhorli release some wonderful research which provides a valuable evidence base on why scores alone are not sufficient. I know the expertise required for the analysis we do at NCSC in the Vulnerability Management Team to ensure we are right when we make the calls we do..
Our findings reveal significant disparities in how scoring systems rank the same vulnerabilities, with implications for organizations relying on these metrics to make data-driven, risk-based decisions. We provide insights into the alignment and divergence of these systems, highlighting the need for more transparent and consistent exploitability, risk, and severity assessments.
https://arxiv.org/abs/2508.13644
Mounting Rowhammer Attacks on DDR4 Servers with ECC Memory
Nureddin Kamadan, Walter Wang, Stephan van Schaik, Christina Garman, Daniel Genkin and Yuval Yarom undermine a mitigation..
Tackling this challenge, in this paper we demonstrate the first end-to-end Rowhammer technique effective against Intel servers using Hynix DDR4 ECC memory. To that aim, we first characterize the Hynix implementation of Target Row Refresh (TRR) on server parts, demonstrating effective hammering patterns on both FPGA and Intel-based testing platforms with ECC disabled. We then reverse engineer Intel’s ECC implementation on Skylake and Cascade Lake servers. We find that it has a coding distance of four, which often allows triggering incorrect ECC correction with just two bit flips. Combining the two observations, we present an end-to-end Rowhammer attack which can flip bits on Intel servers, without causing crashes. Finally, we demonstrate the effectiveness of our attack by hammering RSA public keys loaded into memory, causing the server to accept messages not signed by the original key
Client-Side Deanonymization Attacks on Privacy Sandbox APIs
Eugene Lim show there continues to be a way to go here..
While the
chrome_abt_popvalue may not appear to be particularly sensitive, this is a full demonstration of fully leaking a Shared Storage value cross-origin.
https://spaceraccoon.dev/client-side-deanonymization-attacks-privacy-sandbox-apis/
CVE-2025–41688: Bypassing Restrictions in an OT Remote Access Device
Marcel Rick-Cen shows that we still have a long way to get OT out of the 90s in terms of cyber security.
This OT remote access device is trusted across OT environments in Europe to maintain PLCs, HMIs, and field devices. Under the hood, it runs embedded Linux, exposes a web interface, and offers Lua scripting for automation and diagnostics. A critical vulnerability in the device’s Lua runtime — an undocumented function —bypasses all sandboxing restrictions and allows arbitrary OS command execution as root.
Cisco Secure Firewall Management Center Software RADIUS Remote Code Execution Vulnerability
Patch patch patch..
This vulnerability is due to a lack of proper handling of user input during the authentication phase. An attacker could exploit this vulnerability by sending crafted input when entering credentials that will be authenticated at the configured RADIUS server. A successful exploit could allow the attacker to execute commands at a high privilege level.
Offense
Attack capability, techniques and trade-craft.
A tag to rule them all: Using AWS tags to enumerate cloud resources
Bleon Proko details a technique that defensive teams will want to ensure they have detections for as a leading indicator..
Infrastructure Enumeration is the process of gathering information about a target, after gaining initial access. Enumeration depends on the level of privileges an attacker gets on the initial compromise. For AWS, privileges are split by API call, so if an identity can has a policy that only allows access to
iam:ListUsers, they are not allowed to execute any other API call (except forsts:GetCallerIdentity, but that is allowed by default to all identities).To enumerate resources, an identity will need to know what access they have on the account and then know how what resources can be accessed. Due to how AWS manages privileges and API calls, this will result in many failed attempts and logs generated, which might tip off a defender.
Blocking EDRs traffic
Jony Schats blocks EDRs and creates a case for true signal to exist to support detection engineering.. that a ensuring you have logging of new firewall rules..
WindowsDefenderFirewall.exe
Creates inbound and outbound block rules in Windows Defender Firewall for blacklisted EDR processes.
WindowsFilteringPlatform.exe
Creates WFP filters that block traffic for blacklisted EDR processes. Includes a custom AppID resolution routine to obtain executable identities.
https://github.com/0xJs/BlockEDRTraffic
GroupPolicyBackdoor
Quenn Roland and Wilfried Bécard create a cause for detection engineers to assemble and ensure coverage as it can be expected a range of real-world actors will adopt this into their arsenal.
GroupPolicyBackdoor is a python utility for Group Policy Objects (GPOs) manipulation and exploitation. GPO attack vectors can very often lead to impactful privilege escalation scenarios in Active Directory environments. And yet, offensive security professionals may be reluctant to leverage them, partly due to the perceived risks associated with GPO manipulation.
GroupPolicyBackdoor aims at providing a modular, stable and stealthy exploitation framework for GPO attack vectors, all in python.
https://github.com/synacktiv/GroupPolicyBackdoor
A Guide and Script Collection for Mythic Eventing
Gavin Kramer brings business process automation to red teaming..
Mythic Eventing automates repetitive tasks during red team operations (RTO). This blog documents the eventing system and provides a collection of starter YAML scripts for reconnaissance and other common tasks. These can be modified to execute specific commands or Beacon object files (BOFs) based on your needs. The repository for these scripts are located here:
Hijacking multi-agent systems in your PajaMAS
Suha Sabi Hussain shows how this attack class works in practice which should hopefully inspire detection development if not the application of anomaly detection.
Today, we’re releasing pajaMAS: a curated set of MAS hijacking demos that illustrate important principles of MAS security. In this post, we’ll walk through each demo, explain the underlying security principles, and present concrete guidance for secure MAS development.
MAS hijacking manipulates the control flow of MASs by exploiting how agents communicate with each other. Discovered by Triedman et al., this attack can be seen as a variant of prompt injection that targets MAS control flow. The researchers hijacked multiple MASs to execute arbitrary malicious code, discovering that these attacks succeed:
Across different domains, mediums, and topologies;
Even when individual agents have strong prompt injection defenses; and
Even when individual agents explicitly recognize the prompt as unsafe.
https://blog.trailofbits.com/2025/07/31/hijacking-multi-agent-systems-in-your-pajamas/
Don’t Phish-let Me Down: FIDO Authentication Downgrade
Yaniv Miron shows why you shouldn’t allow fallback / downgrades when deploying phishing resistant.
FIDO-based passkeys remain a highly recommended authentication method to protect against prevalent credential phishing and account takeover (ATO) threats.
Proofpoint researchers have found that FIDO-based authentication can be side-stepped using a downgrade attack.
Using a dedicated phishlet, attackers could downgrade FIDO-based authentication to less secure methods, exposing targets to adversary-in-the-middle (AiTM) threats.
Proofpoint researchers have yet to observe FIDO authentication downgrade attacks in the wild.
Authentication downgrade remains a key method for challenging “phishing-resistant” authentication methods, but attackers’ current focus remains on accounts with other MFA methods or no MFA methods at all.
Related Okta Evilginx phishlet (OIE) with MFA downgrade rewrites
gist.github.com/rotarydrone/15164763bed13f89fceabb4b4089de03
Sauron
Juan Antonio sets a challenge for detection of this tool..
When you obtain fresh credentials (password spraying, phishing, hash replay, etc.), the first thing you need is context: Who is this account really? What groups (direct and nested) does it belong to? Which OUs does it live in? What descriptions reveal its function or linked applications? Sauron answers that in seconds with a single execution.
Primary objective: quickly convert an isolated credential into a mental map of potential capabilities within AD and third-party software/services that reuse corporate groups or descriptions.
https://github.com/sikumy/sauron
SpearSpray
Juan Antonio writes the business case for passkeys and conditional access with this tool.
SpearSpray is an advanced password spraying tool designed specifically for Active Directory environments. It combines user enumeration via LDAP with intelligent pattern-based password generation to perform controlled and stealthy password spraying attacks over Kerberos.
https://github.com/sikumy/spearspray
SpeechRuntimeMove
A neat technique which again you can imagine may be picked up by some criminal actors.
Lateral Movement via SpeechRuntime DCOM trigger & COM Hijacking.
This Proof of Concept (PoC) for Lateral Movement abuses the fact, that some COM Classes configured as
INTERACTIVE USERwill spawn a process in the context of the currently logged on users session.
https://github.com/rtecCyberSec/SpeechRuntimeMove
Exploitation
What is being exploited..
Patching for persistence
Christina Johns, Chris Brook and Tyler Edmonds show that adversary patching is a thing..
[We] detected an adversary executing discovery commands on dozens of cloud-based Linux endpoints vulnerable to a critical remote code vulnerability (CVE-2023-46604) in Apache ActiveMQ, a widely used, open source message broker written in Java.
Red Canary observed the adversary carry out malicious activity on a handful of the endpoints. Follow-on adversary command and control (C2) tools varied by endpoint and included Sliver, and Cloudflare Tunnels to maintain covert command and control over the long term.
In one instance, after exploiting the endpoint and installing the Sliver implant—granting the adversary unrestricted access to the system—they modified the existing
sshdconfiguration file to enable root login. This setting is usually set to deny root login over SSH by default in modern Linux distributions. Allowing root logins enables the adversary remote access with the highest level of privilege. Under a new session started bysshd, the adversary downloaded and executed a previously unknown downloader that we have named “DripDropper.”Finally, the adversary used
curlto download two ActiveMQ JAR files fromrepo1[.]maven[.]org, a domain belonging to Apache Maven. These two JAR files constitute a legitimate patch for CVE-2023-46604. By deleting the existing JAR files and replacing them, the adversary effectively patched the already compromised system.
https://redcanary.com/blog/threat-intelligence/dripdropper-linux-malware/
Fortinet FortiSIEM Pre-Auth Command Injection (CVE-2025-25256)
Sina Kheirkhah releases an exploit for this vulnerability..
Pre-Auth RCE Chains in Commvault
We can expect ransomware affiliate interest in these..
Even so, this chain will likely still impact many CommVault instances. And if it doesn’t, the first chain we described remains unaffected by these limitations.
It’s also worth noting that many CommVault administrators don’t use the built-in
adminaccount at all, which could leave this attack path viable for longer.
Tooling and Techniques
Low level tooling and techniques for attack and defence researchers…
Exploration of logical vulnerability identification based on SAST combined with large models
Chinese experiments and a hint of what is to come..
We tested the vulnerability in an internal testing range project that included 10 known logic vulnerabilities (covering various types, such as price manipulation, unauthorized access, and SMS bombing).
The evaluation results are as follows:
Recall: This solution successfully discovered six of the logical vulnerabilities, achieving a recall rate of 60%. The four vulnerabilities that were not discovered primarily involved extremely complex business state understanding across multiple service calls, and are areas for future optimization.
Accuracy: Of the six vulnerabilities discovered, five were manually verified as real, valid vulnerabilities, for an accuracy rate of 83%. There was one false positive, primarily due to the agent misjudging the indirect effects of a purification function during complex business logic deduction. This was achieved thanks to the ReAct framework's rigorous chain-of-evidence verification process, but it also highlights its limitations in deep logical understanding.
Improved efficiency: The entire automated audit process takes an average of approximately 25 minutes. In comparison, a manual audit of the same scope typically requires at least four working hours (half a working day). This solution is calculated to be nearly 10 times more efficient than manual audits.
Report quality: The generated report contains a clear chain of evidence and directly applicable repair code suggestions, and provides a proof of concept (POC) for verification. It can then be connected to other tools to form a gray-box model for cross-validation.
https://mp.weixin.qq.com/s/pFrGBYpve4ejtjgjrAly_A
Slice: SAST + LLM Interprocedural Context Extractor
Caleb Gross takes us one step closer to our AI enabled vulnerability research future building on Sean Heelan’s work..
If you haven’t read Sean’s post, do. For my own part, a few areas for future work stuck out to me:
How to decide which potentially vulnerable code to send to an LLM?
How to maintain a high signal-to-noise ratio and prevent false positives while expanding the scope of our search?
How to realistically incorporate today’s models into a researcher’s workflow?
I built Slice (SAST + LLM Interprocedural Context Extractor) to address these questions.
We’ll show how Slice works by walking through a reproduction of discovering CVE-2025-37778.
https://noperator.dev/posts/slice/
Headless Ghidra MCP Server for Project-Wide, Multi-Binary Analysis
Clearbluejar takes us one step closer to our AI enabled malware analysis future..
This post introduces pyghidra-mcp, a new headless Model Context Protocol (MCP) server for Ghidra designed for automation.
It exposes an entire Ghidra project for analysis, enabling an LLM to trace function calls across multiple interdependent binaries in a single session.
https://github.com/clearbluejar/pyghidra-mcp
Certifiably robust malware detectors by design
Pierre-Francois Gimenez, Sarath Sivaprasad and Mario Fritz document what robust/secure/resilience malware detection models may look like..
This article focuses on the robustness of machine-learning models against blackbox adversarial attacks in the context of malware analysis. In this domain, adversarial attacks are not required to rely on imperceptible perturbations but need to preserve the semantics of malware. Such attacks typically rely on semanticspreserving transformations, like API call addition or n-grams modification. We propose to use manually selected features with a monotonic model to obtain a robust by design classifier. We also characterize robust classifiers and deduce a framework named ERDALT that can use adversarial examples to train a linear layer that selects non-fragile features. This model is empirically robust by design, meaning that with enough adversarial examples, it converges to a robust classifier. In future work, we will adapt ERDALT to other security-related data, such as robust classifiers of network packets or robust malware dynamic analysis.
https://arxiv.org/abs/2508.10038
Footnotes
Some other small (and not so small) bits and bobs which might be of interest.
Annual, quarterly and monthly reports
Nothing overly of note this week
The Department of Energy’s Unclassified Cybersecurity Program – 2024
Digital Assets Custody Standard - Capital Markets and Technology Association Switzerland publish
SS7: Securing a Legacy Protocol in a Modern Threat Landscape, and how information sharing can help to mitigate - GSMA publish
Artificial intelligence
In-depth: The 2025 Intelligent Security Operations (AI SOC) Market Landscape
LLMs vs. Geolocation: GPT-5 Performs Worse Than Other AI Models
CertTA: Certified Robustness Made Practical for Learning-Based Traffic Analysis - “CertTA incorporates a novel multi-modal smoothing mechanism that explicitly accounts for attack-induced perturbations during the generation of smoothing samples, based on which CertTA rigorously derives robustness regions that are meaningful against these attacks.”
THOR: Secure Transformer Inference with Homomorphic Encryption
Books
Nothing overly of note this week
Events
Defense Software for a Contested Future: Report Release Webinar, August 28th - “At the request of the Defense Advanced Research Projects Agency (DARPA), the National Academies of Sciences, Engineering, and Medicine conducted a study to explore how to enhance the assurance and agility of large-scale, integrated software-based systems. The report recommends ways the Department of Defense can engineer and manage its software systems to reduce cyber risk and enable more rapid system evolution to meet changing mission needs.”
Finally finally the NCSC’s podcast series.
Unless stated otherwise, linked or referenced content does not necessarily represent the views of the NCSC and reference to third parties or content on their websites should not be taken as endorsement of any kind by the NCSC. The NCSC has no control over the content of third party websites and consequently accepts no responsibility for your use of them.
This newsletter is subject to the NCSC website terms and conditions which can be found at https://www.ncsc.gov.uk/section/about-this-website/terms-and-conditions and you can find out more about how will treat your personal information in our privacy notice at https://www.ncsc.gov.uk/section/about-this-website/privacy-statement.